- Courses
 Business Management
Business Management IT Networks and ITSM
IT Networks and ITSM Data Management
Data Management Software Development
Software Development Digital Transformation
Digital Transformation Graphic Design
Graphic Design
- Learning Paths
- Vendors






The F5 Certified™ Professionals program helps you develop career-advancing technical skills and extensive knowledge of F5 products and solutions, including options emphasizing Administration, Sales, Product Specializations, and Solutions including Cloud and Security.
In this 4 day course, students are provided with a functional understanding of how to deploy, tune, and operate ASM to protect their web applications from HTTP-based attacks.
Course Topics
Chapter 1: Setting Up the BIG-IP System
Chapter 2: Traffic Processing with BIG-IP
Chapter 3: Web Application Concepts
Chapter 4: Common Web Application Vulnerabilities
Chapter 5: Security Policy Deployment
Chapter 6: Policy Tuning and Violations
Chapter 7: Attack Signatures
Chapter 8: Positive Security Policy Building
Chapter 9: Cookies and Other Headers
Chapter 10: Reporting and Logging
Chapter 11: Lab Project 1
Chapter 12: Advanced Parameter Handling
Chapter 13: Policy Diff and Administration
Chapter 14: Using Application-Ready Templates
Chapter 15: Automatic Policy Building
Chapter 16: Web Application Vulnerability Scanner Integration
Chapter 17: Layered Policies
Chapter 18: Login Enforcement, Brute Force Mitigation, and Session Tracking
Chapter 19: Web Scraping Mitigation and Geolocation Enforcement
Chapter 20: Layer 7 DoS Mitigation and Advanced Bot Protection
Chapter 21: ASM and iRules
Chapter 22: Using Content Profiles
Chapter 23: Review and Final Labs
Course Objectives
This course is intended for security and network administrators who will be responsible for the installation, deployment, tuning, and day-to-day maintenance of the Application Security Manager.










We have been in the market since 1995, and we kept accumulating experience in the training business, and providing training for more than 200,000 trainees ever since, in Egypt, and the MENA region.
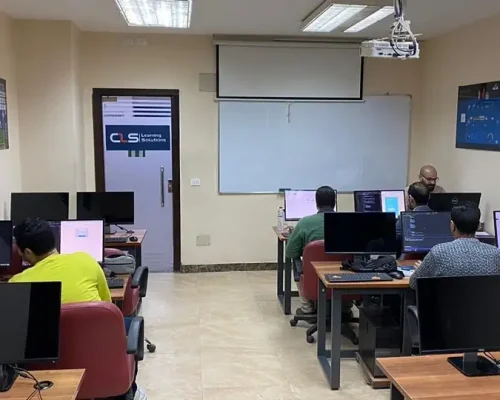
CLS facilities are well-equipped with strong hardware and software technologies that aid both students and trainers lead very effective smooth training programs.
We provide our clients with the best solutions, customized to their specific needs and goals. Our team is highly qualified to answer whatever questions you have.
CLS is an authorized and accredited partner by technology leaders. This means that our training programs are of the highest quality source materials.
We keep tabs on every change in the market and the technology field, so our training programs will always be updated up to the World-class latest standards, and adapted to the global shape-shifting job market.
We select the best instructors, who are certified from trustworthy international vendors. They share their professional experience with the Trainees, so they can have a clear hands-on experience.






























I`m attending now CEH Training with Eng Mohamed Hamdy ,CISSP Training with Eng Mohamed Gohar, I really learned a lot from him , everything here in CLS is very satisfying including facilities .
We took a series of courses as the digital Transformation Unit of the ministry . we just finished CRISC Certification Training with DR Adel Abdel Meneim . Thank you CLS for all your efforts, we really appreciate it
Me and my colleagues are working in a government Organization, We took a no. of cyber security trainings with CLS starting with CEH and CISSP. we liked every thing the instructors, the stuff and whole environment
I`m attending ASP.NET Core with MVC Training with Eng Mohamed Hesham , I really learned a lot from him , everything here in CLS is very satisfying including facilities .Thanks you all team.
Qualifying the cadres of digital transformation units in government agencies moving to the administrative capital .Thanks CLS
I`m attending ASP.NET Core with MVC Training with Eng Mohamed Hesham , I really learned a lot from him , everything here in CLS is very satisfying including facilities .Thanks you all team.
I`m attending now CRISC Training with DR Adel Abdel Meneim , I really learned a lot from him , everything here in CLS is very satisfying including facilities , locations and the team.
I`m attending ASP.NET Core with MVC Training with Eng Mohamed Hesham , I really learned a lot from him , everything here in CLS is very satisfying including facilities .Thanks you all team.

Seize the moment, Learn with CLS, The Top-Rated Training Provider in Egypt since 1995, 28 Years of Experience Training Businesses and People in Egypt and Mena region.
© 2024 - CLS Learning - Solutions | All Rights Reserved.